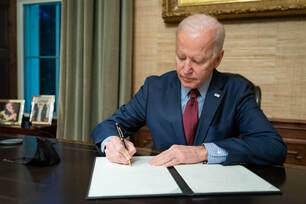
 By Michelle A. Schaap, Team Leader, Privacy & Data Security Practice Chiesa Shahinian & Giantomasi PC We do not have to read the Fact Sheet issued by the White House Briefing Room to know that the cybersecurity practices of Federal agencies and their vendors have been put to the test in the last several months and found to be wanting. Among the breaches we know about: the SolarWinds’ Orion compromise, which went undetected for more than 8 months; Microsoft Exchange’s vulnerability; and the Colonial Pipeline ransomware attack have left exposed the Nation’s lacking coordination when it comes to proactive measures, supply chain cyber resilience, breach detection capabilities, and incident response in the face of ongoing cyber-attacks whether from nation-states or cyber criminals. To address these very real concerns and risks, President Biden’s May 12 Executive Order will require software vendors and cloud providers that wish to continue to be awarded and/or to maintain sought-after government contracts to meet security standards that are consistent across agencies, and which require transparency, zero trust architecture, and mandatory reporting of breaches. As a cybersecurity attorney, I see the measures outlined in the Order to be necessary and appropriate in light of the ongoing attacks to our private and public sectors. Moreover, I hope these measures lead to national standards that ultimately replace the current patchwork quilt of thirty-plus proactive laws adopted by different states and disparate agencies’ procurement standards. The policy and goals set by the Executive Order are to improve the Federal government’s ability to “identify, deter, protect against, detect and respond” to cybersecurity threats, vulnerabilities, incidents and breaches. The policy further highlights the critical importance in this war against cyber-crime of the sharing of information between the public and private sectors, and will apply to federal agencies and their on-premises, cloud-based and hybrid resources. The end result will be that in approximately one year’s time, federal agencies will be required to implement best practices to secure their systems and software and, further, will require their software and cloud providers to do the same – both contractually and in practice. Agencies will be migrating to secure cloud environments and will be required to remove products and solutions that do not meet the final cybersecurity rules and criteria amending the Federal Acquisition Regulation (FAR). Legacy software will need to be updated unless a waiver is granted – and then only on a case-by-case basis. The expectation is that a standardized federal agency playbook for incident response and better, more coordinated threat gathering and sharing will enable federal agencies to prevent, detect, contain and respond more effectively to the cyber threats that continue to threaten our virtual shores and systems. Additionally, the Order will develop the IoT cybersecurity equivalent to the Consumer Product Safety Commission’s labeling requirements for consumer goods. It has been suggested that the private sector will follow the government’s lead and begin taking a closer look at its cloud providers’ and software vendors’ security and cybersecurity practices, even in the absence of legislation mandating this assessment. As such, companies in the space should be prepared for: • Requiring sharing of risk information • Mandatory reporting of cyber incidents • Required multi-factor authentication and encryption • Required disclosure of software components Those companies that cannot demonstrate that they have taken a privacy-by-design approach to their products and solutions and do not have a cybersecurity program in place may find that their customer prospects will be diminishing. Now is the time then for these companies to take stock and improve their posture on data protection and risk mitigation.
2 Comments
6/10/2021 07:38:56 am
Michelle, great insights and recommendations for private companies to consider. Multi-factor authentication is being added to underwriting requirements to secure a Cyber Liability policy.
Reply
Michelle, your insights on cybersecurity standards are invaluable. Implementing robust measures like multi-factor authentication is paramount in safeguarding against evolving cyber threats. Your recommendations are pivotal for private companies navigating this increasingly complex landscape.
Reply
Leave a Reply. |
Guest Blog
Archives
May 2024
Categories |
- About Us
- Events & Programs
-
Forums
- Diversity, Equity & Inclusion Forum
- Environmental Business Council
- Family-Owned Business Forum
- Healthcare Foum
- Higher Education Forum
- Human Resources Forum
- International Forum
- Manufacturing Forum
- Marketing Forum
- Next Gen: A Young Professionals Organization
- Non-Profit Forum
- Real Property Forum
- Technology for Business Forum
- Transportation Forum
- Women in Commerce Forum
- Membership
- COMMERCE Magazine
- Member Directory
- Member News
- Guest Blog
|
Copyright Commerce and Industry Association of New Jersey. All Rights Reserved.
365 West Passaic Street Suite 490 | Rochelle Park, NJ 07662 Phone: (201) 368-2100| [email protected] | sitemap |

 RSS Feed
RSS Feed
